Relay Attack Car Theft: How Thieves Steal Vehicles & How to Protect Yourself

Modern vehicles are smarter than ever.
Keyless entry, push-to-start ignition, and proximity-based unlocking have made owning and operating a car more convenient. But like most conveniences, these advancements have also introduced new vulnerabilities, ones that criminals are actively exploiting.
One of the fastest-growing threats today is known as a relay attack.
These attacks don’t involve breaking windows, forcing doors, or hot-wiring a vehicle. In fact, many victims don’t even realize what happened until their car is already gone.
Instead, relay attacks rely on signal extenders (also called relay amplifiers or boosters) to trick your vehicle into thinking your key is present.
And it works.
What Is a Relay Attack?
A relay attack is a type of wireless exploit that targets vehicles equipped with Passive Keyless Entry (PKE) systems.
These systems are designed to detect when your key fob is nearby. When the vehicle senses the key, it automatically unlocks doors and allows the engine to start.
The problem? The vehicle doesn’t verify who has the key. Iit only verifies that the signal exists.
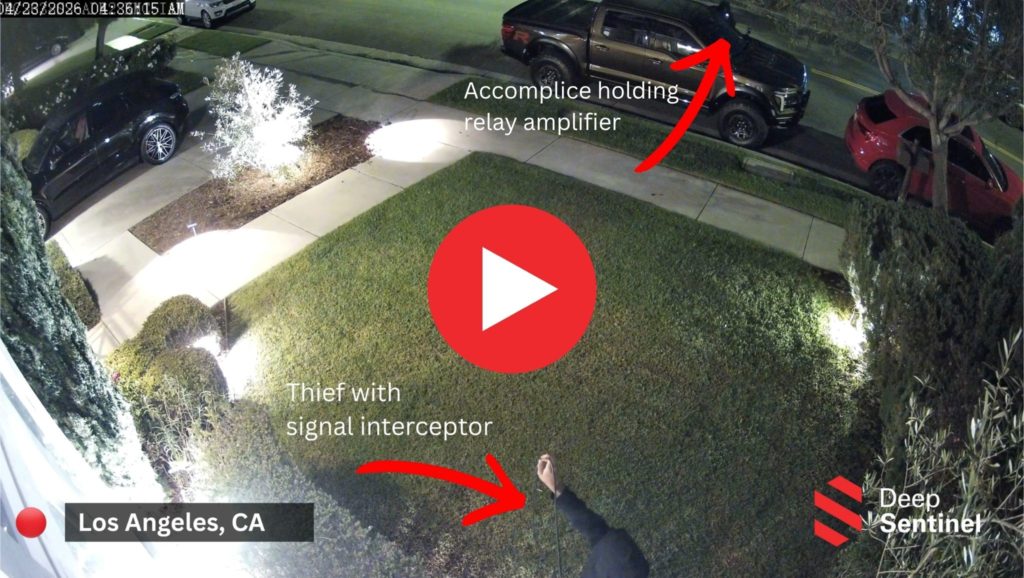
That’s where attackers step in. Watch the video below or click here to see a relay attack in action.
How Signal Extenders Work
A signal extender, or relay device, is used to capture, amplify, and transmit the signal from your key fob over a longer distance.
Even if your key is inside your home, in your pocket, or on your kitchen counter, these devices can make your vehicle believe it’s sitting right next to the car.
How the Attack Happens (Step-by-Step)
Relay attacks are typically carried out by two individuals working together.
STEP 1: Signal Interception
One thief positions themselves near your home, garage, or wherever your key fob is located. Using a signal interceptor (essentially an antenna), they capture the weak radio signal emitted by your key fob.
STEP 2: Signal Transmission
That captured signal is wirelessly transmitted to a second device held by an accomplice standing near your vehicle.
STEP 3: Signal Amplification
The second device amplifies the signal, tricking the vehicle into believing the key fob is within range.
STEP 4: Access and Theft
The vehicle unlocks. The engine starts. No alarm. No broken glass. No visible forced entry.
The entire process can take under two minutes.
Who is at Most Risk?
While any vehicle with keyless entry can be targeted, some scenarios increase risk significantly.
1. Vehicles Parked in Driveways or Street
Cars parked outside are easier targets than those secured inside garages.
2. Keys Stored Near Entry Points
If your key fob is near a front door, window, or wall, it becomes easier for attackers to capture the signal.
3. Dense Residential Areas
Townhomes, apartments, and neighborhoods with close proximity make it easier for attackers to operate unnoticed.
4. Higher-End Vehicles
Luxury vehicles are more frequently targeted due to resale value and demand.
Why Awareness Matters More Than Ever
Many people assume that because there’s no visible break-in, the risk is low. In reality, the opposite is true.
Relay attacks are growing because:
- The tools are inexpensive and widely available
- The method is easy to replicate
- The success rate is extremely high
And unlike older methods, these attacks scale easily across neighborhoods.
How to Reduce Your Exposure
While no system is completely immune, there are several practical steps you can take to significantly reduce your risk.
1. Store Keys in Faraday Pouches
Faraday pouches block radio signals from your key fob, preventing interception. This is one of the simplest and most effective protections.
2. Keep Keys Away from Doors and Windows
Avoid placing keys near entry points where signals can be easily captured from outside.
3. Disable Passive Keyless Entry (If Possible)
Some vehicles allow you to turn off keyless entry features. While less convenient, it removes the attack vector entirely.
4. Use Physical Barriers
Parking in a garage adds an extra layer of protection. Even basic deterrents can increase the effort required for attackers.
5. Add Visible Security Measures
Cameras, lighting, and surveillance systems increase the likelihood that suspicious behavior is detected early.
6. Stay Informed About Local Activity
If thefts are happening nearby, your risk increases immediately. Awareness allows you to act proactively.
The Role of Real-Time Intervention
One of the biggest challenges with relay attacks is timing.
Because the theft happens so quickly, prevention must happen before or during the attempt—not after. This is where real-time detection and intervention, through a system like Deep Sentinel, become critical.
If suspicious behavior—such as individuals approaching a vehicle late at night—is identified early, intervention can disrupt the attack entirely. In many cases, simply being seen or challenged is enough to cause attackers to abandon the attempt.
Why Traditional Security Falls Short
Most traditional security systems are designed to respond after an event occurs.
- Alarms trigger once a door is opened
- Cameras record footage for later review
- Notifications arrive after the fact
But relay attacks don’t trigger alarms. There’s no forced entry. No break-in.
That means detection needs to shift from reactive to proactive.
What This Means Going Forward
As vehicles continue to evolve, so will the methods used to exploit them. Relay attacks are just one example of how modern technology can be repurposed in unintended ways. The key takeaway is simple: Convenience should never come at the cost of awareness.
Understanding how these attacks work—and how you may be exposed—is the first step in protecting yourself.